IT acronyms and abbreviations: Your quick reference guide
Decode the most important acronyms in information technology, from APIs and VPNs to ERP and MFA. Get a simple explanation of the terms that power your digital operations.

Browse acronyms by category
Networking, IT infrastructure and core technology
AI and machine learning
AI
Artificial Intelligence
AI refers to systems that perform tasks requiring human-like reasoning. It’s used in analytics, automation, chatbots and complex decision support.
AIOps
AIOps: Artificial intelligence for IT operations
AIOps uses AI and machine learning to identify incidents and optimize performance. It helps teams detect issues faster and automate remediation.
GenAI
Generative artificial intelligence
GenAI creates new content such as text, images or code. It’s increasingly used in automation design, documentation generation and customer experience tools.
ML
Machine learning
ML analyzes data to identify patterns and make predictions. Organizations use ML for forecasting, anomaly detection and personalization.
MLOps
Machine learning operations
MLOps manages the full lifecycle of machine learning models from development through production. It ensures models remain accurate and reliable over time.
NLP
Natural language processing
NLP enables machines to interpret and generate human language. It supports chatbots, document processing and conversational AI systems.
Automation and orchestration
API
Application programming interface
An API allows applications to communicate using standardized requests. APIs support real-time data movement and automation across modern systems.
BPA
Business process automation
BPA automates tasks and workflows that support business operations. It helps reduce manual effort while improving accuracy and speed.
BPM
Business process management
BPM is the discipline of mapping and optimizing business processes. It provides visibility into how work moves through systems and teams.
CI/CD
Continuous integration and continuous delivery
CI/CD automates the build, test and deployment stages of software development. It helps teams ship updates faster and reduce errors.
DevOps
Development operations
DevOps bridges development and IT operations through collaboration and automation. This model increases reliability and reduces deployment risks.
DPA
Digital process automation
DPA extends BPA by automating complex, multi-step workflows. It combines process design, orchestration and analytics to improve operations at scale.
IA
Intelligent automation
IA blends automation with AI, analytics and machine learning. Organizations use IA to make workflows adaptive and self-improving.
I&O
I&O: Infrastructure and operations
I&O teams manage compute, storage, networks and service delivery. Their work underpins the reliability of all technology services.
ITPA
IT process automation
ITPA automates routine IT tasks like provisioning, patching and backup. It frees teams to focus on strategic projects rather than maintenance.
LCNC
Low code / no code
LCNC tools let users build workflows and applications with minimal programming. They enable business users to automate tasks independently.
MFT
Managed file transfer
MFT provides secure, auditable file movement across systems and partners. It’s critical for compliance-driven industries and high-volume data flows.
Rest API
Representational state transfer
A REST API is a lightweight design for web-based integrations. It’s widely used for cloud services, mobile apps and microservices architectures.
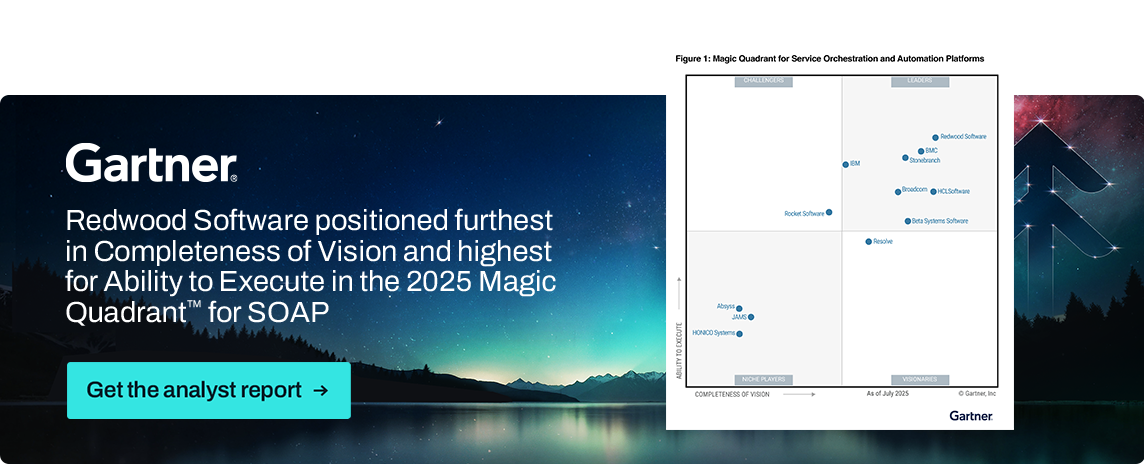
SOAP
Service orchestration and automation platform
A SOAP platform orchestrates IT, data and business processes end to end. It connects applications, cloud environments and databases through centralized automation.
WLA
Workload automation
WLA schedules and executes jobs across applications, servers and cloud services. It ensures critical business processes run on time.
WLA&O
Workload automation and orchestration
WLA&O expands WLA with cross-system workflows and real-time event triggers. It provides full visibility and governance across complex automation chains.
Cloud computing
APIM
Application programming interface management
APIM manages APIs throughout their lifecycle, from design to deployment. It helps teams control access, performance and security across cloud and hybrid environments.
BPaaS
Business process as a service
BPaaS delivers business processes like HR, finance or procurement through the cloud. It helps organizations reduce manual work and implement real-time automation without deploying traditional software.
DaaS
Data as a service
DaaS provides access to data streams or datasets on demand through cloud APIs. It supports analytics, BI dashboards and AI models by making high-quality data easier to access.
DX
Digital transformation
DX is the modernization of systems, tools and processes using digital technologies. It often includes automation, cloud migration and new operating models.
FTP
File transfer protocol
FTP is a legacy protocol for transferring files between servers. While still used in some environments, it’s often replaced by more secure options like SFTP or MFT.
HTTP
Hypertext transfer protocol
HTTP is the foundation of communication on the web. It enables browsers, APIs and applications to exchange information over the World Wide Web.
IaaS
Infrastructure as a service
IaaS delivers compute, storage and networking over the cloud. It allows IT teams to scale environments quickly without managing physical hardware.
IoT
Internet of Things
IoT refers to connected devices that exchange data over networks. These devices power real-time monitoring in areas like smart manufacturing, logistics and energy.
iPaaS
Integration platform as a service
iPaaS connects applications, data sources and cloud platforms through prebuilt connectors. It helps organizations integrate systems without heavy custom coding.
PaaS
Platform as a service
PaaS provides cloud environments for building and deploying applications. Developers use PaaS to build software without managing servers or infrastructure.
SaaS
Software as a service
SaaS delivers applications through the internet rather than installed locally. It supports fast updates, predictable pricing and simpler IT operations.
SASE
Secure access service edge
SASE combines networking and security functions into a cloud-native service. It helps organizations support remote work and secure access from any location.
SFTP
SSH file transfer protocol
SFTP transfers files securely using encrypted SSH connections. It’s widely used for systems integration, data pipelines and compliance-heavy workloads.
VM
Virtual machine
A virtual machine emulates a complete computer system through software. IT teams use VMs to run workloads independently of physical hardware.
XaaS
Anything as a service
XaaS refers to any service delivered through a cloud model. It covers everything from infrastructure to analytics and full business functions.
ZTNA
Zero trust network access
ZTNA restricts access based on identity, device posture and context. It enables a zero-trust security model where no user or device is inherently trusted.
Data and analytics
APM
Application portfolio management
APM tracks and optimizes applications across the organization. It helps teams understand usage, cost and value.
BI
Business intelligence
BI tools analyze data to generate insights, dashboards and reports. They support strategic decision making and operational visibility.
CRM
Customer relationship management
CRM systems manage sales, marketing and support interactions. They help organizations track relationships and improve customer experience.
DBMS
Database management system
A DBMS stores, organizes and retrieves structured data. It ensures data consistency, performance and security across applications.
ETL
Extract, transform, load
ETL pulls data from sources, shapes it and loads it into a target system. It’s foundational for analytics, BI and machine learning pipelines.
ERP
Enterprise resource planning
ERP systems unify core business functions like finance, supply chain and HR. They provide a single source of truth for operational data.
OLAP
Online analytical processing
OLAP supports complex analytical queries and multidimensional analysis. It’s used for forecasting, budgeting and advanced reporting.
OLTP
Online transaction processing
OLTP systems handle real-time transaction data such as orders or payments. They are optimized for speed, reliability and high volumes.
Networking, IT infrastructure and core technology
CPU
Central processing unit
The CPU executes instructions that power applications and services. It determines overall system performance across personal computers and virtual machines.
DNS
Domain name system
DNS maps domain names to IP addresses. It functions as the address book of the internet and keeps web traffic routed correctly.
HTML
Hypertext markup language
HTML structures content on the web. It works with CSS and JavaScript to build pages, apps and digital experience.
ICT
Information and communication technology
ICT refers to the technologies and systems used to store, access and transmit information across networks. It includes telecommunications, computers, software, data infrastructure and the digital tools organizations rely on for modern operations.
IP address
Internet protocol address
An IP address uniquely identifies a device on a network. It enables communication between computers, servers and cloud applications.
ISP
Internet service provider
An ISP delivers internet connectivity to homes and businesses. They also provide DNS, routing and network support.
LAN
Local area network
A LAN connects devices within a limited area such as an office or building. It supports fast communication, file sharing and internal applications.
NAS
Network-attached storage
NAS provides centralized file storage that users can access over a network. It supports backups, file sharing and media storage.
OS
Operating system
An OS manages system resources and runs applications. Examples include Windows, Linux and macOS.
PC
Personal computer
A PC is a computer designed for individual use. It’s used for productivity, browsing, development and business applications.
RAM
Random access memory
RAM stores data that a computer needs to access quickly. It plays a major role in performance for applications, operating systems and virtual machines.
SQL
Structured query language
SQL is a programming language for managing and querying databases. It underpins data analytics, BI and application development.
UID
Unique identifier
A UID is a numeric or alphanumeric code that uniquely identifies a record or device. It’s used in authentication, asset tracking and information systems.
VPN
Virtual private network
A VPN secures connections between users and networks through encrypted tunnels. It protects sensitive data and supports remote work.
WAN
Wide area network
A WAN links multiple locations or data centers across long distances. It enables organizations to operate reliably across regions.
Security and compliance
CISO
Chief information security officer
The CISO oversees cybersecurity strategy and governance. This role ensures that systems, networks and information remain protected from evolving threats.
DAM
Database activity monitoring
DAM monitors database activity to detect abnormal or unauthorized access. It strengthens data security and helps organizations meet compliance requirements.
IDS
Intrusion detection system
An IDS scans network and system activity for suspicious behavior. It alerts cybersecurity teams when potential threats emerge.
MFA
Multi-factor authentication
MFA requires users to verify their identity using more than one method. It strengthens access control and reduces the risk of unauthorized access.
NIST
National Institute of Standards and Technology
NIST creates cybersecurity, encryption and risk management frameworks. Organizations rely on NIST standards for secure system architecture
SLA
Service-level agreement
An SLA defines performance expectations between a customer and a service provider. It outlines availability targets, response times and support requirements.
SSH
Secure shell
SSH provides secure remote access and encrypted communication. It’s widely used for system administration and file transfers.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally, and MAGIC QUADRANT is a registered trademark of Gartner, Inc. and/or its affiliates and are used herein with permission. All rights reserved.
These graphics were published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from https://www.advsyscon.com/resource/gartner-mq/.







